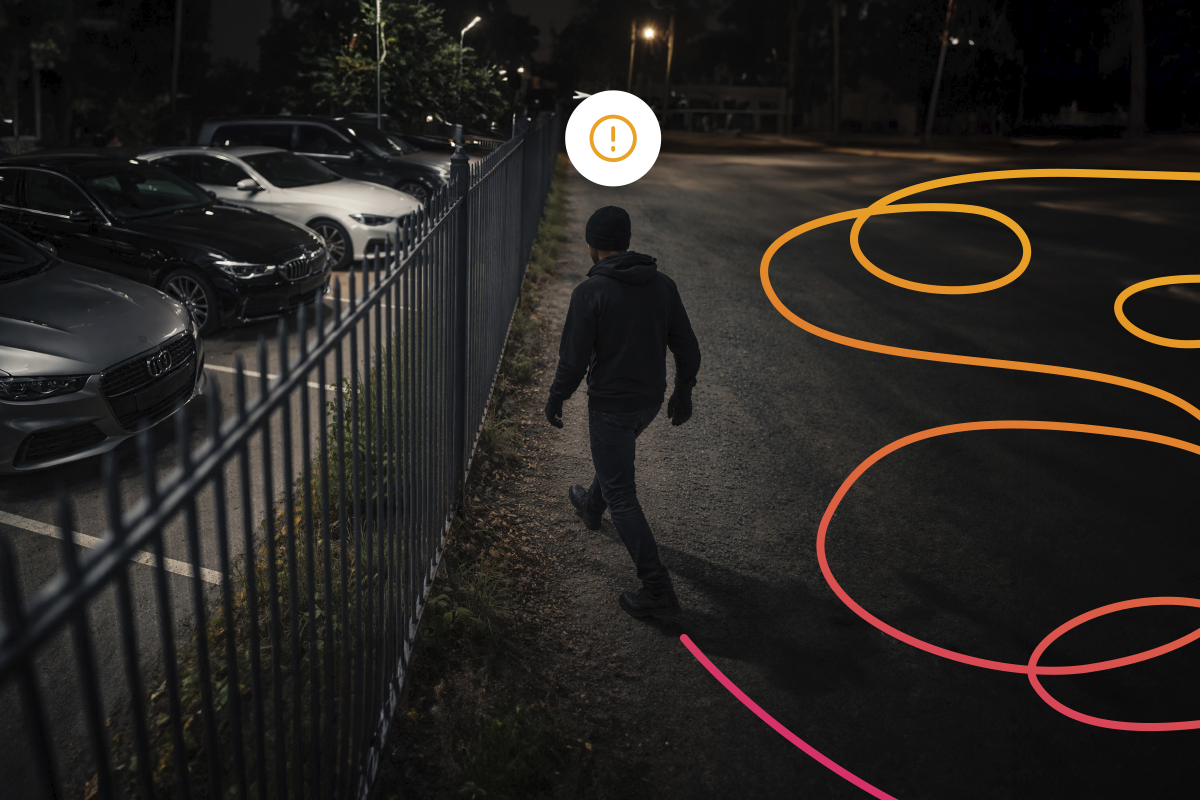
What is loitering?
Loitering describes a behaviour in which a person remains in or moves around an area without a clear purpose, observing the surroundings or repeating paths. This type of conduct may precede security incidents, although on its own it does not imply any criminal action.
Its detection is complex, as it is often mistaken for normal activity, especially in environments with a constant flow of people.
Where does it occur?
Loitering can appear in any space with public circulation, such as:
- Shopping centres
- Car parks
- Airports and stations
- Hospitals
- Offices and corporate buildings
- Hotels
- Sports facilities
- High street retail areas
In these environments, distinguishing between normal and suspicious behaviour is particularly difficult without automated tools.
Limitations of traditional video surveillance
Conventional systems present several limitations when it comes to detecting loitering:
- They do not analyse behaviour over time
- They rely on constant human monitoring
- They struggle to identify subtle or repetitive patterns
- They generate reactive rather than preventive responses
As a result, many incidents are only identified once they have already occurred.
The solution: DFUSION /3
DFUSION /3 incorporates AI-based video analytics to identify loitering patterns in real time.
Its approach is not based on detecting isolated events, but on analysing behaviour through multiple combined conditions using its advanced rules system (Super rules). This allows detection to be adapted to each environment and use case.
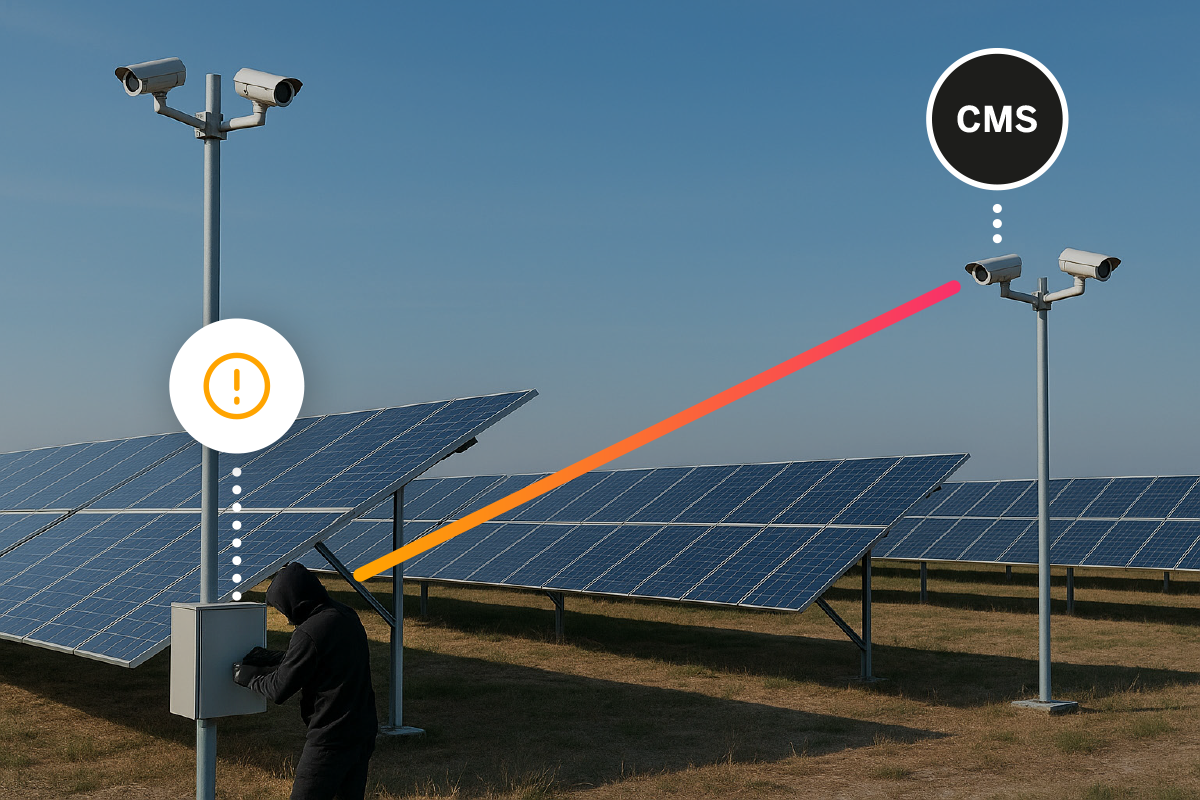
What can it detect?
- Prolonged presence in specific areas
- Repetitive or directionless movements
- Presence in sensitive areas out of context
- Behaviours that, when combined, indicate potential risk
Operational benefits
- Early detection of potentially problematic situations
- Improved decision-making with greater contextual awareness
- Reduced operational workload for security personnel
- Greater efficiency in monitoring multiple cameras
- Adaptability to different environments and needs
Value for each profile
End user
- Greater control over their environment
- Improved perceived and actual security
- Incident prevention
Installer / partner
- Easy integration into existing systems
- Flexible configuration through rules
- Application across multiple sectors
- Technical support and project guidance